What Is Zero Trust Security for Small Business and Should You Actually Care?
Zero Trust security for small business is not enterprise theatre. It is a practical way to stop attackers turning one stolen password or one weak device into a full business-wide problem.
What is Zero Trust security for small business?
Zero Trust is a security approach built around explicit verification, least-privilege access, and assuming a breach can happen.
In plain English, Zero Trust security for small business means nobody gets a free pass just because they signed in once, connected from the office, or know the Wi-Fi password. Users, devices, locations, and sessions are checked continuously using the signals your systems already have.
Trust nothing by default. Verify everything. Limit access everywhere.
Why the old model falls over
Older cyber security models assumed there was a safe inside and a risky outside. That falls apart when staff work remotely, cloud apps sit on the public internet, and business data is accessed from laptops, phones, home offices, and third-party platforms.
Once an attacker has valid credentials, the question is no longer whether they can break in. The real issue is what else they can reach after login. That is why Zero Trust focuses so heavily on contextual authentication, device health, privilege restriction, and continuous monitoring.
Password-first access
If a password is stolen and nothing else is enforced, the attacker may already be halfway in.
Unmanaged devices
Unmanaged endpoints can become an easy entry point if device health is not checked properly.
Privilege spread
Broad admin rights and poor separation make one compromised account much more dangerous.
Why small businesses should care
Small businesses rely on cloud email, Microsoft 365, accounting platforms, CRMs, shared files, and remote access just as much as larger organisations. That means they face the same identity, device, and access risks even if the environment is smaller.
The practical controls are straightforward. Strong multi-factor authentication, controlled admin rights, healthier devices, and better visibility all reduce the impact of the most common compromise paths.
| Question | Reality | Zero Trust response |
|---|---|---|
| We are too small to be targeted | Attackers usually go for whoever is easiest to compromise, not whoever is biggest. | Harden identity, devices, and access before size becomes irrelevant. |
| We trust our staff | Zero Trust is about compromised accounts and devices, not doubting your team. | Verify continuously without making work painful. |
| We already have a firewall | That does little if an attacker logs straight into your cloud services. | Make login controls and device posture part of your front line. |
What Zero Trust looks like in practice
Zero Trust security for small business is usually a stack of sensible controls, not a giant rip-and-replace project. The goal is to verify users and devices properly, reduce unnecessary access, and keep better visibility over what is happening.
How to implement Zero Trust security for small business
This is the part that matters. You do not need enterprise bloat. You need a staged rollout that fixes the obvious gaps first, then adds more depth where it counts.
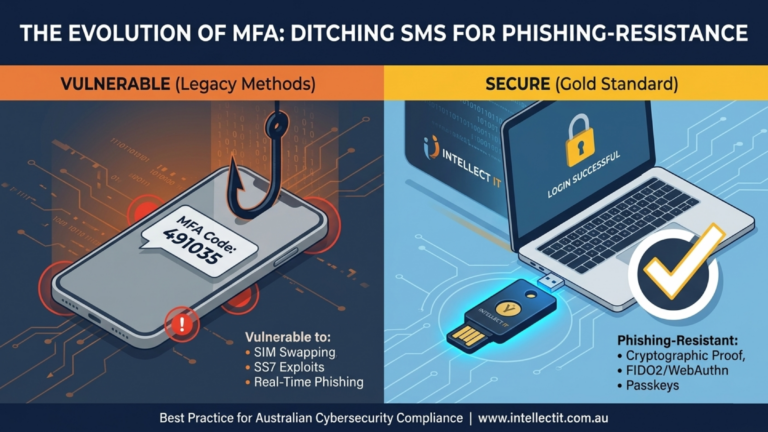
Enforce MFA where it matters most
Start with business-critical systems, email, admin accounts, and remote access first.
Trust devices only when they prove they are healthy
Use encryption, anti-malware, OS version controls, and compliance checks before access is granted.
Cut admin rights hard
Use separate privileged accounts, remove unnecessary access, and keep emergency access tightly controlled.
Use context in access decisions
Think about identity, device compliance, location, app sensitivity, and risk rather than relying on a password alone.
Centralise logs and actually watch them
Authentication changes, suspicious sign-ins, and new privileged accounts often reveal trouble early.
Test backup and recovery
Assume something will go wrong eventually and make sure your containment and recovery path actually works.
Best quick wins for Intellect IT clients
For a small business already using Microsoft 365, the best starting moves are usually MFA enforcement, Conditional Access baselines, endpoint compliance, admin-role cleanup, and tighter sign-in monitoring.
Those changes improve security quickly without forcing a full infrastructure rebuild. They are practical, measurable, and much easier to justify to a business owner than abstract security theory.
FAQs
Is Zero Trust just a buzzword for enterprise?
No. The core controls are practical and directly address common small-business risks such as stolen credentials, unmanaged devices, excessive access, and poor visibility.
What is the first thing a small business should do?
Start with MFA on the systems that matter most, then reduce admin rights, verify device compliance, and monitor sign-ins properly.
Does Zero Trust slow staff down?
Not when it is configured properly. The goal is to add stronger checks where they matter most without adding pointless friction everywhere.
Can this work with Microsoft 365?
Yes. Microsoft 365 is often one of the best places to start because identity, access control, device posture, and monitoring can all be layered together in a practical way.
Ready to reduce cyber risk across your business?
If your team relies on Microsoft 365, remote access, cloud apps, and shared business data, stronger identity, access, and device controls can make a real difference. Intellect IT helps businesses put practical protections in place without unnecessary complexity.
- Tighten access controls around critical systems
- Improve visibility over sign-ins and privileged activity
- Reduce reliance on broad admin permissions
- Support a stronger, more resilient security posture